Resources
The Go-To Knowledge Base for IT and Cybersecurity Insights and Information
The American Technology Services (ATS) Resource Hub is your central access point for essential IT knowledge. Here, you’ll find an extensive collection of materials designed to keep you informed and prepared in the rapidly transforming tech landscape. From in-depth analyses and practical guides to expert insights, our internally authored resources are meticulously curated. Explore our resource hub to access content. Explore our resource hub to access a wealth of carefully curated content, including in-depth articles, practical guides, expert insights, and valuable tools designed to support your business needs.
Articles
Stay updated with the latest industry insights.
Our blogs cover the latest trends, news, and tips in the tech world. From cybersecurity updates to IT management best practices, our blog posts are crafted by industry experts to keep you informed and ahead of the curve. Stay engaged with regular updates and thought-provoking articles designed to spark innovation and enhance your IT strategies.
Case Studies
Real-world success stories and solutions.
Discover how ATS has helped businesses like yours overcome challenges and achieve their goals. Our case studies provide detailed accounts of our solutions in action, showcasing the impact of our services across various industries. Learn from real-world examples and see how our expertise can translate into success for your organization.
Datasheets
Detailed specifications for informed decisions.
Our datasheets offer a comprehensive look at our services’ features and benefits. These documents provide technical details and specifications to help you make informed decisions about your IT investments. Explore the depth and capabilities of our offerings with clear, concise information at your fingertips.
eBooks
In-depth knowledge and expert insights.
Dive deeper into key topics with our expertly crafted eBooks. These resources are designed to provide extensive information and insights on a wide range of subjects, from cloud computing to cybersecurity strategies. Each eBook is packed with valuable content that can help you understand complex topics and implement effective solutions.
Infographics
Visual insights for quick understanding.
Our infographics present complex information in an easy-to-understand visual format. These resources are perfect for quickly grasping key concepts and trends without getting bogged down in technical jargon. Enhance your understanding with visually engaging content that distills essential information into clear, concise graphics.
Security Advisories
Critical alerts to safeguard your systems.
Stay ahead of potential threats with our timely security advisories. We provide critical alerts and actionable advice to help you protect your IT infrastructure from emerging risks. Our advisories are designed to keep you informed and prepared, ensuring you can take proactive steps to maintain the security of your systems.
Newsletters
The ATS Cybersecurity Newsletter: Your Weekly Security Intel
Stay in the know with the ATS Cybersecurity Newsletter, your weekly source for expert curated top news on the biggest risks and emerging trends in cybersecurity. We cover everything from software flaws, sophisticated attack methods, and phishing tactics to regulatory updates, offering the insights you need. Don’t settle for surface-level updates—get important cybersecurity intelligence sourced by the ATS Security Operations team.
Cybersecurity Checklists
Awareness, Readiness, Setup, Maintenance
Our cybersecurity checklists are built to challenge assumptions and uncover weak spots across your security program. Whether it’s around-the-clock monitoring, threat exposure, incident response, or vendor risk, each checklist asks the questions that reveal what’s working—and what’s being missed. Whether you’re reviewing internal security practices or preparing for an outside threat, these checklists offer direct, practical insights to help you move from “we think we’re covered” to “we know we are.” Explore the checklists to find out what you might be missing—and how ATS can help close the loop.
Stay Informed, Stay Ahead
The ATS Resource Hub is here to equip you with the knowledge and tools to make informed business decisions regarding IT and cybersecurity. Explore our resources, stay informed, and leverage ATS’ expertise to drive your business forward. Keep checking back for new content and updates that will help you stay at the forefront of technology and innovation.
Featured Articles
Articles / Last night, the American Technology Services New York team bundled up and crunched across the ice to the...
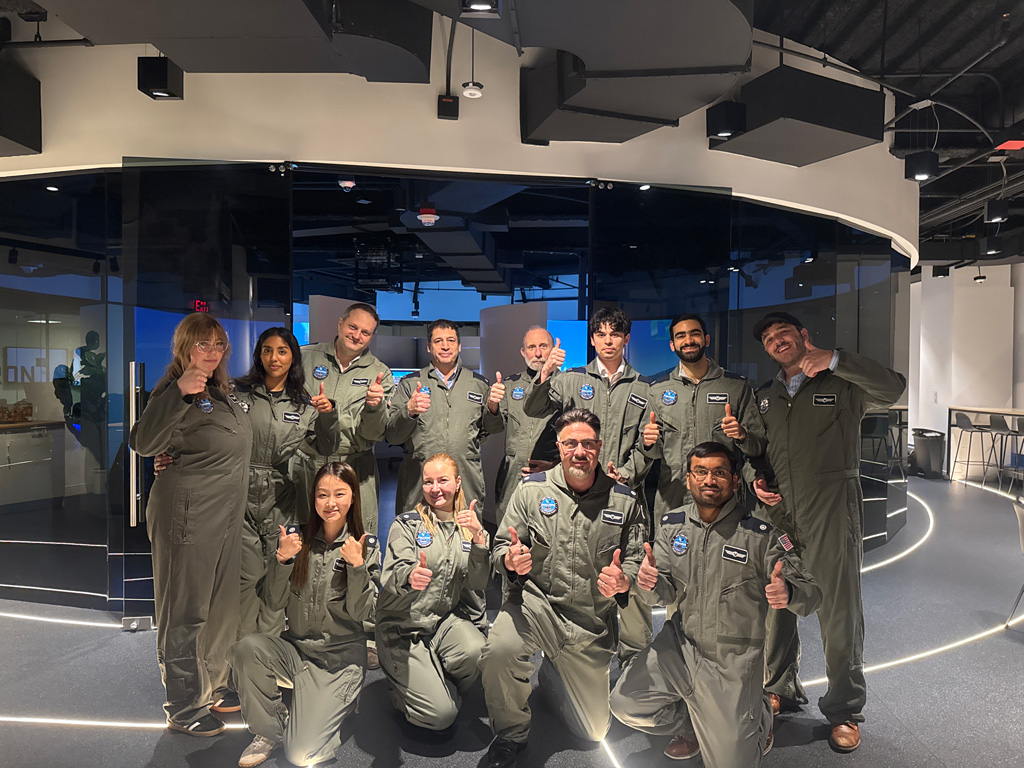
Articles / On June 5, ATS opened its doors for NY Tech Week and turned a 6th-floor downtown office into...
Articles / Businesses and individuals face a rapidly growing menace. Account Takeover (ATO) fraud is a sophisticated cybercrime reaching alarming...
Articles / Businesses are increasingly threatened by Distributed Denial of Service (DDoS) attacks. These attacks are designed to disrupt network...